
In order to create useable shellcode, we need to figure out the canary value. This can be done by using the format string vulnerability. Check C18 for more info (link)
Let’s try to hack it locally first:
gcc final.c -o final -m32 -no-pie

And you got:

….. it leaks some data for sure, but where is the canary value …..
let’s try another method
According to the source code:

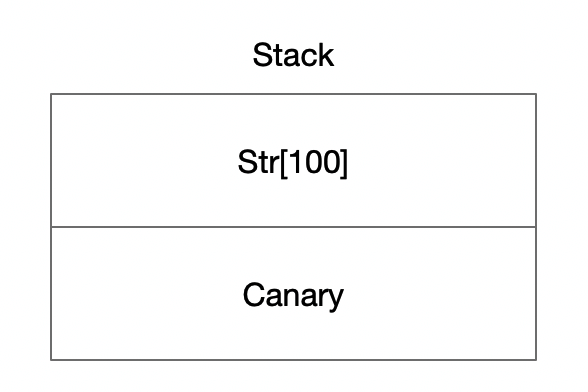
The size of the str array is 100, so let’s fill it with a 100 ‘A’s and then leak the data, because the canary value should be put just right after the array on stack. Like this:
Let’s update the attack script:

And let’s run it:

Haha, found you! 78383025 is the canary value (for this time), and it is the 29th value.
According to this page in C18 (link):

We can directly access any parameter on stack using the dollar sign qualifier. “%4$x” is used which will read the 4th parameter on stack.
In our case, we want to read the 29th parameter on stack, so let’s update our code:

and let’s run the code:

Ah! we go the canary value. Let’s try to create the shellcode with this value.
In order to overflow the code, we need to find the correct length of dummy characters. This can be done easily if there is no StackGuard. So, let it be :)
Now, let’s recompile the source code and disable the StackGuard (remove the canary value).
gcc final.c -o final_without_canary -m32 -no-pie -fno-stack-protector
Run gdb:
gdb ./final_without_canary
Use gdb-peda to generate De Brujin Sequence. (Check C08, page 25) (link)
pattern create 200 pattern200
r < pattern200
It will trigger Buffer overflow, and we got this screen:

Type:
pattern offset $eip
And it shows the offset is 112
OK. Now we know that in order to trigger buffer overflow, the length of our dummy characters should be 112. Like this:

However, the “real” program is with Canary value. And the Canary value is place right after the array. So, we need to change the structure a little bit.

Let’s update our shellcode!
Note that the leaked canary value is in String so we need to convert it to hexadecimal value and then convert it to little endian format. But it’s not that hard.

Let’s run it:

We didn’t get any error and that’s a good sign!
Now it’s your turn, try to complete the shellcode and get the flag :)